Liftoff
Blip Bloop
EK-M.2 NVMe Heatsink Review

Having doing some I/O intensive stuff on my workstation, I was a bit surprised to see the temperatures on my Samsung 960 Pro NVMe M.2 SSD hitting 71C. I never experienced thermal throttling on my SSD, but it is a possibility and when it throttles performance will drop off a cliff as the SSD controller attempts to bring temperatures under control.
Even more confusing is there are two temperature sensors on the SSD – and the only one that is exposed to tools like CrystalDiskInfo is NOT the one that is used to determine when the drive will throttle. In fact, without access to the second temperature secret-squirrel temperature sensor that the drive controller uses to determine what the thermal throttling limits are, users are in the blind and can’t predict when it will happen during heavy write workloads.
I decided to pick up a EK M.2 heatsink for my 950 Pro on Amazon to help combat this potential problem. While I haven’t encountered thermal throttling yet on my workstation, I’d like to keep the SSD cool to prevent this from happening at all.
The kit comes with two clips, two different size strips of thermal pads, an instruction card, and the heatsink plates itself. Installation was very easy. Just cur the strips of thermal pads to fit, and clip the heatsink plates on; then install the M.2 SSD as normal.
Here’s a few pictures of how my 950 Pro looks with the heatsink installed:
Getting Pritunl working with Let’s Encrypt CA
Recently I was working on a fresh install of Pritunl’s VPN server on a VM. Pritunl’s software is free for simple configurations and is a really easy way to setup a VPN server in a few minutes – it’s also compliant with OpenVPN standards so you can use either the ubiquitous OpenVPN client or Pritunl’s own branded client. The Pritunl client has some advantages like easy one-step configuration with a similarly configured Pritunl server (vs importing a settings files) but otherwise they are largely functionally the same.
One of the new features that was recently (within the last year?) added to Pritunl was the ability to use Let’s Encrypt certificates in the server. Previously, you had to either get a third-party plugin or run Pritunl behind a reverse proxy to get Let’s Encrypt or any other certificate working (without upgrading to a more expensive paid license).
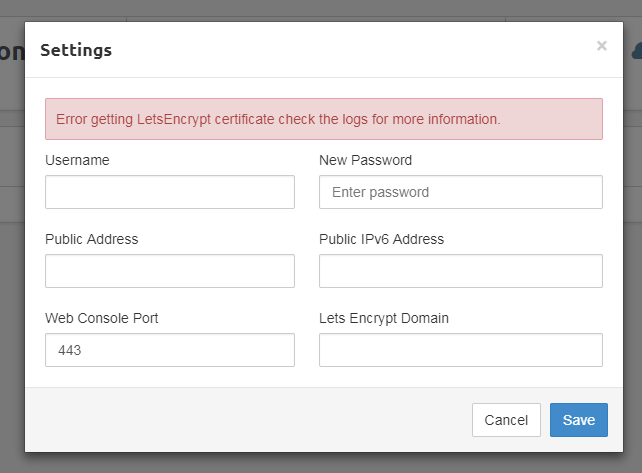
However, the Let’s Encrypt function wasn’t working. Normally, you would set the domain name for the certificate in the settings dialog box, then hit “Save” and the backend would run and verify the domain, fetch the certificate, and apply it all automatically.
Now, I’m just getting “Error getting LetsEncrypt certificate check the logs for more information.”
Okay, lets take a look at the logs:
[patient-plateau-8521][2017-11-16 16:08:58,851][INFO] Parsing acme account key...
[patient-plateau-8521][2017-11-16 16:08:58,981][INFO] Parsing acme CSR...
[patient-plateau-8521][2017-11-16 16:08:59,075][INFO] Registering acme account...
[patient-plateau-8521][2017-11-16 16:08:59,850][ERROR] Failed to get LetsEncrypt cert
Traceback (most recent call last):
File "/usr/lib/pritunl/local/lib/python2.7/site-packages/pritunl/handlers/settings.py", line 711, in settings_put
acme.update_acme_cert()
File "/usr/lib/pritunl/local/lib/python2.7/site-packages/pritunl/acme.py", line 49, in update_acme_cert
cert = get_acme_cert(settings.app.acme_key, csr)
File "/usr/lib/pritunl/local/lib/python2.7/site-packages/pritunl/acme.py", line 24, in get_acme_cert
app.set_acme,
File "/usr/lib/pritunl/local/lib/python2.7/site-packages/pritunl/acme_tiny.py", line 111, in get_crt
raise ValueError("Error registering: {0} {1}".format(code, result))
ValueError: Error registering: 400 {
"type": "urn:acme:error:malformed",
"detail": "Provided agreement URL [https://letsencrypt.org/documents/LE-SA-v1.1.1-August-1-2016.pdf] does not match current agreement URL [https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf]",
"status": 400
}
acme_domain = u'this.is.my.domain'
Oh…great. Um, it looks like there’s a problem with the agreement URL which are basically the Terms of Service for using Let’s Encrypt. The solution was actually very easy.
SSH into the sever and edit the main configuration file:
/usr/lib/pritunl/local/lib/python2.7/site-packages/pritunl/settings/app.py
In my config, it was on line 124. Edit the line to the newest agreement and save and close.
'acme_agreement_url': 'https://letsencrypt.org/documents/LE-SA-v1.2-November-15-2017.pdf',
Re-compile the Python binary and restart the Pritunl server, then try setting your domain name again.
sudo python -m compileall . sudo service pritunl restart
This time it worked like a charm for me. Done!
That New Computer Smell
http://pcpartpicker.com/b/sjyXsY
This build was based on the Dan-Cases A4-SFX mITX case that started it’s life in the [H]ard|OCP forums and evolved into a Kickstarter campaign. The purpose of this build was make a living room computer / custom Steam box but is currently being used as my main PC until I get my 2011v3 build completed.
The GA-Z170N-Gaming 5 motherboard was purchased during Amazon Prime Day at a steep discount and had several months of use in another case stress testing before I put it into it’s home in the Dan-Cases A4-SFX case.
32 GB of RAM was selected to provide plenty of headroom when using creative applications like Premiere and Photoshop.
This build originally stated with a GTX980 but evolved into the GTX1080 because of the long wait for the case’s Kickstarter campaign.
The 950 Pro NVMe SSD was purchased during a coupon campaign from jet.com – I originally wanted to keep the machine fully SSD but the price of a 2TB NVMe SSD was cost-prohibitive.
Due to the low profile requirements to jam a HSF into the case, I selected the Cryorig C7 cooler. However, there was excessive fan noise from this cooler – particularly when overclocked
The processor was then delidded with a Rockit Cool delidding tool and the thermal compound was replaced with Coollaboratory’s Liquid Pro interface material. This was able to provide over a 30 degree drop in temperatures and allowed me to keep the fan speed very low to keep noise down.
How To: Add Certificate To Windows 7 RDP
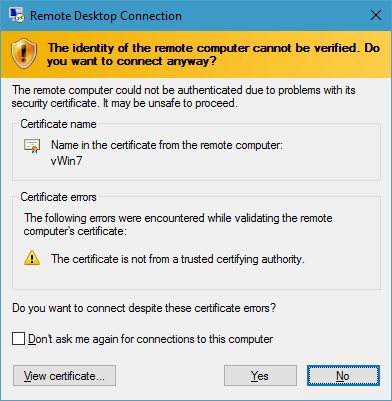
This was more something that was bothering me than anything absolutely necessary, but I wanted to get a properly signed certificate installed on my remote Windows 7 machine that’s hosted in a datacenter as a VM. Every time I connected to it, the RDP client would display an error that the RDP server wasn’t providing a proper security certificate:
More annoying than anything, really. However, since I do have several certificates that are signed this was a problem I could remedy.